Apr 6, 2026
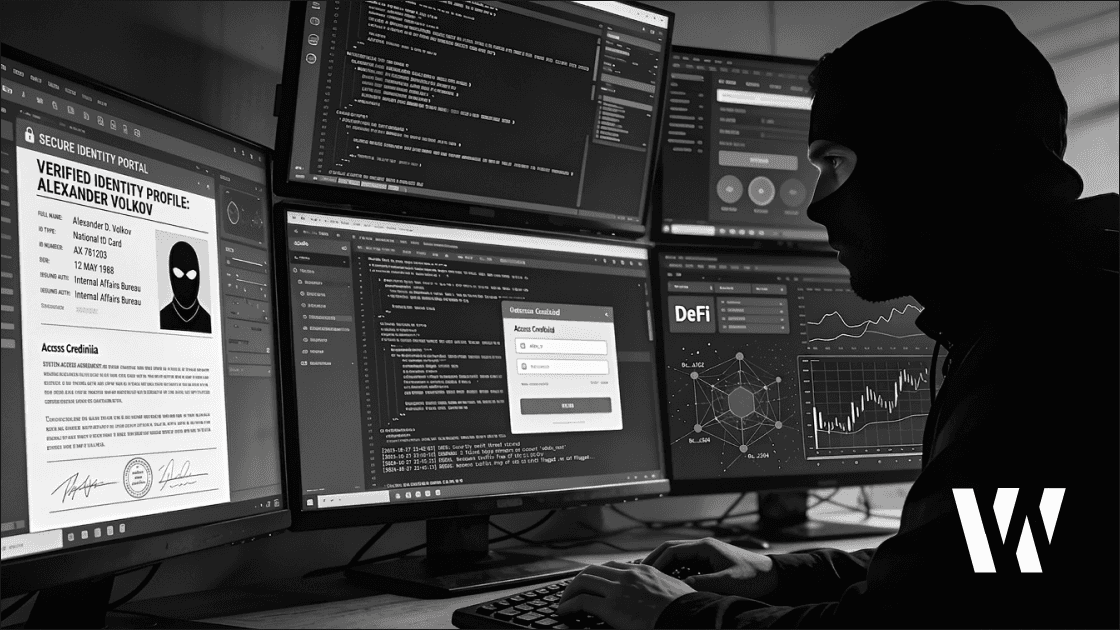
DPRK Developers Infiltrated 40+ DeFi Protocols in April 2026
MetaMask security researcher Taylor Monahan said on April 5, 2026 that North Korean IT operatives had worked inside more than 40 DeFi projects for at least seven years. The disclosure came days after the April 1 Drift Protocol exploit and reframed the story as a long-running insider risk, not just a series of external hacks.
Want the signal behind the headlines? Subscribe to Web Snack - a daily crypto market briefing with sharp analysis, security context, and the stories moving the market.
Context
Monahan’s warning changed the frame around DeFi security. The problem was not simply anonymous wallets attacking from the outside, but trusted contributors gaining access over time while working under fabricated identities.
Her most widely cited point was blunt: “Lots of DPRK IT workers built the protocols you know and love, all the way back to DeFi summer.” She also wrote, “The seven years of blockchain dev experience on their resume is not a lie.” - Taylor Monahan, Security Researcher at MetaMask, April 5, 2026.
The naming of specific protocols made the claim harder to dismiss. Among the projects cited in coverage of Monahan’s findings were SushiSwap, Thorchain, Fantom, Shib, Yearn, and Floki.
Details
The clearest confirmed case in this cycle is Drift Protocol, the Solana-based perpetuals venue exploited on April 1, 2026. Drift used the $280 million figure in its own disclosures, while Elliptic estimated the loss at $286 million based on blockchain analysis.
Investigators said the operation was built over roughly six months. Attackers reportedly approached contributors through the industry, built credibility, deposited more than $1 million into a Drift ecosystem vault, and then abused Solana’s durable nonce feature to push malicious transactions past normal multisig assumptions.
Drift said the attack was linked with medium-high confidence to UNC4736, also tracked as AppleJeus or Citrine Sleet, a DPRK-linked cluster previously associated with the 2024 Radiant Capital hack. Elliptic, TRM Labs, and Diverg separately tied the exploit to North Korean actors, while the stolen assets were bridged from Solana to Ethereum and consolidated into roughly 129,000 ETH across four wallets.
Impact
The Drift exploit matters partly because it sits inside a larger, measurable pattern. Chainalysis-linked reporting put DPRK crypto theft at $2.02 billion in 2025 alone, up 51% from 2024, while the cumulative total since 2017 stood at a $6.75 billion lower bound before 2026 incidents were added.
Washington had already moved against the labor networks behind those operations. On March 12, 2026, the U.S. Treasury sanctioned six individuals and two entities tied to DPRK IT worker schemes that generated nearly $800 million in 2024.
A separate case showed the threat was not limited to protocol hiring. On March 31, Google Threat Intelligence Group said a DPRK-linked actor compromised maintainer access and published malicious Axios npm package versions for about three hours, extending the same operational playbook into software supply chains.
“We interviewed someone who turned out to be a Lazarus operative. Did video calls and was extremely qualified.” - Tim Ahhl, Founder at Titan Exchange, April 5, 2026. His account captured the core security problem: teams were not dealing with low-skill impersonators, but with credible operators able to pass normal screening.
Next Steps
Drift said Mandiant was leading the forensic investigation, but no full recovery timeline had been disclosed as of April 5, 2026. The protocol also used on-chain messages to contact wallets linked to the exploit, while the market waited for firmer disclosure on counterparties and any possible recovery path.
For DeFi teams, the immediate takeaway is operational. Identity checks, contractor onboarding, contributor trust, and developer environment security now sit much closer to the center of protocol risk management than many teams had assumed.
If stories like Drift and DPRK infiltration matter to your edge, subscribe to Web Snack - a daily crypto newsletter covering market moves, risks, and what matters next.
P.S. This article is for informational purposes only and does not constitute investment advice. Always conduct your own research and make independent decisions.
